Secure Shell (SSH) is a network protocol for secure data communication, remote shell services or command execution and other secure network services between two networked computers that it connects via a secure channel over an insecure network. When used to log into a remote system it connects by default over port 22 unlike telnet which uses port 23. While telnet uses plain text authentication, SSH uses encrypted authentication. A SSH Client is typically used to remotely control a system running on SSH server.
SSH can transfer files using the associated SFTP or SCP protocols. SSH uses the client-server model.
SFTP
SSH File Transfer Protocol (also Secret File Transfer Protocol, Secure FTP, or SFTP) is a network protocol used for accessing files, transferring and managing them over any reliable data stream. It was designed by the Internet Engineering Task Force (IETF) as an extension of the Secure Shell protocol (SSH) version 2.0 to provide secure file transfer. It can also be used with other protocols. This protocol assumes that it is run over a secure channel like SSH and the server has already authenticated the client, and that the identity of the client user is available to the protocol.
SCP
The SCP protocol is a network protocol which supports file transfers between hosts on a network. SCP uses SSH for data transfer and utilizes the same mechanisms for authentication, hence transfer of data takes place securely. A client can send (upload) files to a server and clients can also request files or directories from a server (download).
Comparison
| SCP | SFTP |
| It allows only file transfers. | It allows for a range of operations on remote files. SFTP clients include resuming interrupted transfers, directory listings, and remote file removal. |
| Mostly implemented on Unix platforms. | SFTP servers are commonly available on most platforms. SFTP attempts to be more platform-independent than SCP; for instance, with SCP, the expansion of wildcards specified by the client is up to the server, whereas SFTP's design avoids this problem. |
| It is a new protocol designed from the ground up by the IETF SECSH working group. | SFTP is most often used as subsystem of SSH protocol version 2 implementations, having been designed by the same working group. |
SSH IN LINUX
1. USING COMMAND LINE
· CHECKING IF SSH IS INSTALLED OR NOT
In linux, we are very likely to already have a command line SSH program installed on our system. We can check this by typing command:
which ssh
If SSH is not installed we can install it by typing command
sudo apt-get install ssh
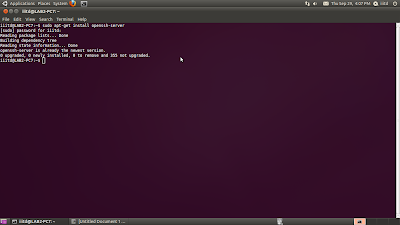
· SETTING UP THE SERVER AND THE CLIENT
First we will setup ssh server on one computer using command
sudo apt-get install openssh-server
Now the server is setup. The next step is to setup a client using command
sudo apt-get install openssh-client
 After setting up the server and the client, we are now ready with the SSH shell and can transfer data securely.
After setting up the server and the client, we are now ready with the SSH shell and can transfer data securely.
ssh username@IPaddress_server (IP address can be found out by typing ifconfig in the terminal)
We can see all the files of the server in the client PC by using command ls.
ls will list all the files on server.
To get a file from server we use the command
get (filename) ( full path of the location on the client)
· SCP
For copying file from server to client, we use the command
scp (filename with full path)username@IPaddress_server:(location on server)
2. USING GUI(GRAPHIC USER INTERFACE)
· We will first install PuTTY.
· We will then start PuTTY by double-clicking the executable file PuTTY.exe that we downloaded.

· The 'PuTTY Configuration' window will open.
· Enter the 'Host Name' field and enter the name (or IP address) of the machine we want to connect to.
· Select the SSH for 'Protocol'.
We can also save the name of the machine for future sessions by clicking on the save button. Next time the name will appear and we can access it by simply clicking on the name.

· On connecting to the machine for the first time, we will be informed with a dialog box saying that the authenticity of the host cannot be established. If we are connecting to the right machine, we need to click on yes.
· We can now transfer files.
We will first download WinSCP and then run the application.

The WinSCP login gets open. As shown below:

Here we are required to fill in the IP address of the machine with which we want to connect, username, password and the private key that we get while installing the software. Then we select the protocol SFTP. And click login.
 We get a window as shown below for verification. Enter yes.
We get a window as shown below for verification. Enter yes.

And now the connection is established and you can access the files of that computer.
For SCP we repeat the same procedure but select the option SCP instead of SFTP.

Again you can see we can view the files on server and copy them.
To exit we simply click on the cross on right hand side corner and select the option OK we want to end the session.








No comments:
Post a Comment